Why a Wrong Config Can Be More Dangerous Than Wrong Code
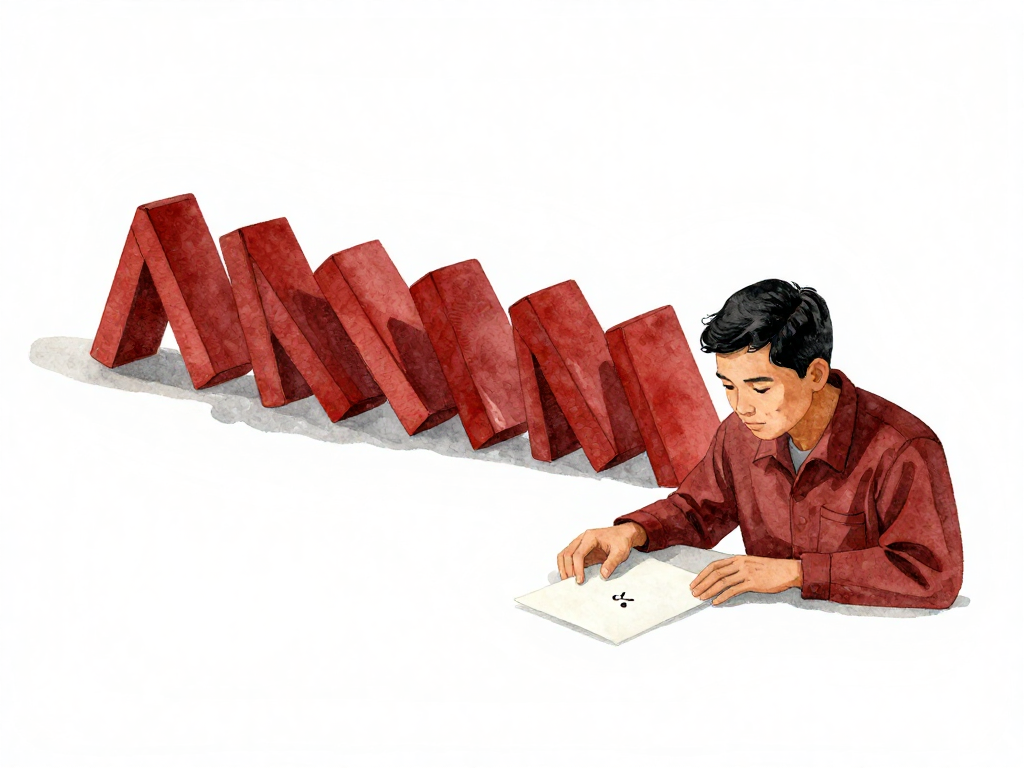
A developer changes one character in a configuration file. The URL db-prod.internal.company.com becomes db-prod.intrnal.company.com. One missing letter. The change gets deployed. Within minutes, every application that tries to connect to the database fails. Login stops working. Search returns nothing. Transactions freeze. The entire application goes down.
There was no bug in the code. No logic error. No algorithm failure. Just a single missing character in a config file.
This scenario plays out in teams more often than most engineers want to admit. And it reveals something uncomfortable: a bad config can cause more damage, faster, than bad code.
The Speed of Impact
When code has a bug, it usually goes through layers before causing visible damage. Input validation might catch it. A conditional check might prevent the wrong path from executing. Error handling might catch the failure and return a graceful response. Even when a code bug reaches production, it often takes time to manifest.
Config is different. Config values are loaded when the application starts. They control connections, timeouts, endpoints, credentials, and feature flags. The moment a wrong config value is loaded, the application acts on it immediately. There is no safety net. There is no graceful degradation when the database URL is wrong. There is no fallback when the timeout value is too low.
Consider another example: someone changes a connection timeout from 30 seconds to 3 seconds. The intention was reasonable—fail fast when something is wrong. But in production, the database sometimes takes 5 seconds to respond under load. Now every legitimate request times out. The application looks unstable. The database team says everything is fine. The engineering team spends hours debugging code that has no issues. The problem was in a single number in a config file.
Config Errors Are Harder to Trace
When code breaks, developers have tools. Stack traces point to the exact line. Logs show the sequence of events. Error messages often describe what went wrong. The debugging process has a clear starting point.
Config errors leave almost no trace. The application stops working. There is no stack trace because no code executed incorrectly. There is no error message because the application could not even reach the point where error handling exists. The application just sits there, refusing to connect, refusing to respond, refusing to give any clue about what went wrong.
Teams can spend days chasing bugs in the codebase, running tests, reviewing recent commits, only to discover that the problem was in a config file changed two weeks ago by someone who no longer remembers making the change.
Multiple Hands, No Coordination
Config files get touched by many people. Developers change database URLs for local testing. DevOps engineers modify ports for deployment configurations. DBAs rotate credentials for security compliance. Platform engineers adjust resource limits. Each change seems small and harmless at the moment. Each change is made without the same rigor applied to code changes.
Nobody reviews a config change the way they review a code change. Nobody validates whether the new value makes sense in context. Nobody checks whether the change was tested in staging. The config file becomes a collection of unverified assumptions, each waiting to fail at the worst possible moment.
The Real Danger Is Invisibility
The most dangerous aspect of config errors is that they often go unnoticed until they cause real damage. A wrong URL in a development config file might sit there for weeks. Nobody notices because the development environment is not under constant load. Then someone copies that config to staging, and tests start failing. The team blames the tests. They debug the test framework. They check the code. Days later, someone notices the URL.
This invisibility makes config errors more insidious than code errors. Code errors surface during development, during code review, during testing. Config errors hide in plain sight, waiting for the right conditions to strike.
Treat Config Like Code
The solution is not complicated, but it requires a shift in mindset. Config must be treated with the same discipline as code. Every config change should go through the same process:
- Code review by another person
- Format validation against a schema
- Value sanity checks
- Testing in a staging environment before production
This is not about bureaucracy. It is about recognizing that config is not a second-class citizen in the delivery process. Config is a delivery artifact that can bring down an entire system with a single character error.
Practical Checklist for Config Changes
Before deploying any config change, run through this quick checklist:
- Has someone else reviewed the change?
- Is the format validated against a schema?
- Are all URLs, ports, and endpoints reachable from the target environment?
- Are timeout values reasonable for the expected load?
- Have credentials been rotated recently and updated in all environments?
- Was the change tested in a non-production environment?
- Is there a rollback plan if the config causes issues?
This checklist takes two minutes. It can save hours of debugging and prevent production outages.
The Takeaway
Config errors are faster, harder to trace, and more invisible than code errors. One missing character can take down an entire application. One wrong timeout value can make a healthy system look broken. Config is not a detail to be handled casually. It is a critical delivery artifact that deserves the same rigor as code. Treat it that way, or prepare for the debugging sessions that follow.